
Hello ️⛷️😊,
I’ll see you again for the March edition of Récap’IT.
March was a busy month in the cybersecurity world. State-sponsored attacks are evolving, the supply chain has become a prime target, NIS2 is ramping up, and identities remain at the heart of all threats. Here’s what you need to know.
Enjoy your reading!
📅📅 On the agenda today:
NIS 2: Finally, more information
👉Go!!
Before we begin, I invite you to follow us 👉

NIS2: the time for theory is over. Since March 17, 2026, ANSSI has made available the Cyber France Reference Framework—ReCyF—which lists the recommended measures for achieving the security objectives set by NIS2. This working document, published by Vincent Strubel himself, is the near-final catalog of organizational and technical measures that critical and important entities will need to implement. While not immediately mandatory, it nevertheless allows those who apply it to cite it in the event of an ANSSI audit.
What stands out upon reading the report is that identity and access governance is at the heart of the requirements. The HID 2026 State of Security and Identity report, based on feedback from more than 1,500 IT professionals, confirms this: 73% of respondents now rank identity management as their top strategic priority, with the convergence of physical and logical access becoming the norm. The obstacles remain the same—budget constraints for 51%, integration complexity for 37%—but fragmented architectures are becoming increasingly difficult to justify in the face of regulatory requirements.
For CIOs affected by NIS2, the message is clear: the ReCyF is not just another document to file away. It is the framework you should use to map out your roadmap starting now.

Receive the best IT news of the month.
Market trends, IT trends, cyberattacks in France... a summary of the news
One in four SMEs has suffered a data breach in the past twelve months, despite budgets that can exceed 250,000 euros annually. This is the paradox highlighted in the 2026 edition of the Proton Report on SME Cybersecurity, which surveyed 3,000 decision-makers across six countries. In France, the average budget allocated to cybersecurity is €27,000 per year, yet 222,250 French companies were reportedly victims of a cyberattack last year, according to the study’s projections.
The problem isn't a lack of awareness or tools. 73% of French SMEs have conducted a formal risk assessment within the past year, and more than half review their security posture monthly or quarterly. 92% already have security measures in place. What is lacking is execution: implementing security with real human expertise requires much more than simply deploying tools. The consequences are tangible: 39% of attacked companies lost data, 31% experienced a business shutdown, and 23% had funds stolen—with financial losses ranging from €4,250 to €84,000, often equivalent to an entire year’s security budget.
So the question is no longer "Are we investing enough?" but "Are we investing in the right places?"
Without experts to monitor the system, interpret alerts, and respond at the right moment, the budget remains just a line item on a ledger—not a shield.
Source: ITmanager, Cybersecurity


Attackers are now exploiting valid credentials to gain access to systems, rendering traditional defenses less effective. Once access is gained, the attack progresses extremely quickly: over the past twelve months, the average lateral movement time has been 29 minutes, with a recorded minimum of 27 seconds, according to CrowdStrike. This is one of the key findings from the Gartner IAM Summit 2026, held in London on March 9 and 10. The overall message is clear:identity become the primary perimeter to defend.
The vendors in attendance all agreed on the same priorities: comprehensive visibility into access, governance of non-human identities—AI agents, service accounts, APIs—and a gradual shift away from traditional MFA toward phishing-resistant mechanisms. On average, organizations are only aware of about half of the devices accessing their applications, as 1Password pointed out. What you can’t see, you can’t protect.
On the issue of tool selection, Gartner was keen to clarify the proper use of its own Magic Quadrant. The best vendor is, above all, the one that aligns with each organization’s needs and use cases, emphasized Brian Guthrie, an analyst and research director at Gartner. Only 60% of the vendors in the quadrant offer 99.99% availability, and orchestration capabilities remain unevenly deployed. In other words: being a leader in a Magic Quadrant does not mean being the right choice for your specific context.
Source: ICT Journal, ICT Journal (2)


Major supply chain breaches have nearly quadrupled since 2020, according to IBM’s 2026 X-Force Threat Intelligence Index. The modus operandi is well-known: attackers no longer launch direct attacks. They target interconnected systems and trusted integrations—suppliers, open-source dependencies, CI/CD workflows, and cloud interfaces—to slip into production environments using legitimate access credentials. SaaS isn’t the problem. Ungoverned access is.
By 2026, the supply chain will become a continuous operational metric. Annual questionnaires and self-reported audits will give way to requirements for proof: dependency monitoring, shared metrics, and access traceability. Every supplier, every API, and every integration represents an extension of the risk scope. The question isn’t whether your third parties use SaaS—that’s a given. The question is: do you know exactly who is accessing what, with what permissions, and since when?
Source: IBM, Digital Solutions
Would you like to receive our white paper on identity and access management?

Cyberattacks linked to geopolitical tensions are changing in nature. They no longer seek to extort—they seek to destroy. The attack by the Iranian group Handala against Stryker in March 2026 illustrates this starkly: tens of thousands of workstations wiped clean, operations paralyzed in 79 countries, with no ransom demand. ANSSI confirms this in its 2025 Cyber Threat Panorama: France remains under constant pressure from state-sponsored actors —led by Russia and China—targeting critical infrastructure for espionage and offensive positioning.
What these attacks have in common is their modus operandi. They do not rely on sophisticated malware but on stolen credentials and legitimate administrative tools —RDP, PowerShell, WMI—to move freely within networks once access has been gained. No exotic malware. Just a network that’s too flat.
For CIOs, the conclusion is clear: perimeter security is no longer enough. Limiting access rights to only those systems that are actually managed, segmenting privileged accounts, and detecting abnormal east-west traffic—these are the factors that determine resilience against such attacks.
Source: BleepingComputer, L'Informaticien


The CVE program, the global vulnerability database that nearly came to an abrupt halt in 2025 due to a lack of funding, has now been secured for the long term. CISA and MITRE have renegotiated a structural agreement: CVE is shifting from a discretionary budget line to a protected budget line. The crisis has been resolved—but it at least had the merit of raising the question Europe had been avoiding: can we allow a critical global cybersecurity infrastructure to depend on a single U.S. contract? ENISA launched its own vulnerability database in May 2025. A first step toward an answer.
Source: LeMondeInformatique

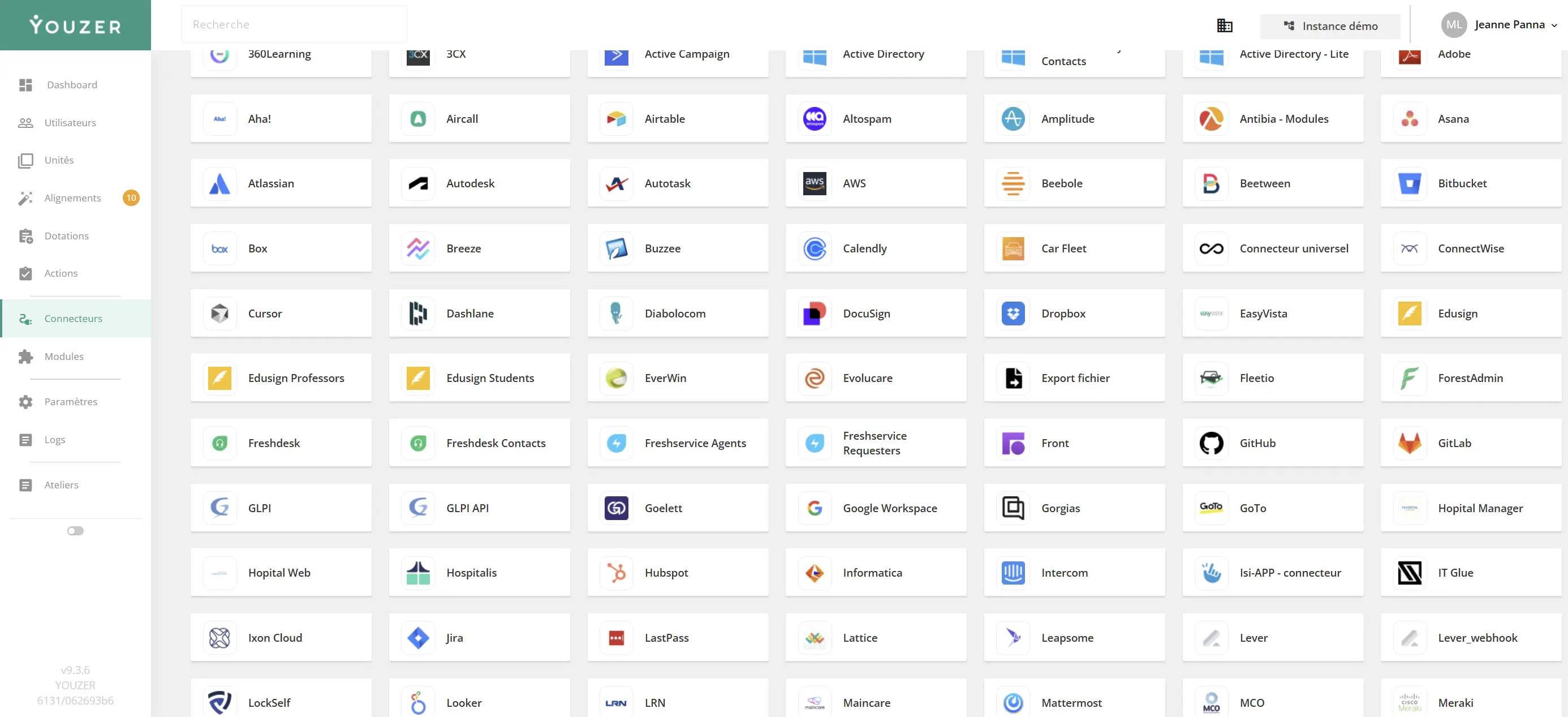
Connectors are the gateway to Youzer: they automatically sync user accounts from your various tools with your identity repository. In practice, Youzer connects to your applications to determine who has access to what—and triggers the necessary actions: creating, modifying, suspending, or deleting accounts.
The catalog now covers the main categories of SI tools:
The catalog is constantly expanding to meet customer demand. And for tools not yet listed, the universal connector steps in: based on CSV file exchanges or API calls, it allows you to connect any application not natively supported—without having to wait for a dedicated connector to be developed.
Thank you for reading me this far!
Any feedback, want to discuss a project?
I'm here for that 👋.
We've sent you the newsletter and you think it's great? Sign up here 👇
Sharing this newsletter is what keeps it alive!
Every month I send you my discoveries, my analysis on IT news.
I do a lot of monitoring and I share it all!
I'm Mélanie and I'm Youzer's marketing manager.
About me? I have an unquenchable thirst for learning! I'd rather read a book 100 times than watch a movie. I'm a fan of HP 🧙🏼.
I do running and collective sport roller (don't look for it, it's dangerous).