📢 Webinar: Review of Authorizations: Simple for IT, Seamless for Approvers – June 23 at 11 a.m. Register here ✅

Hello ️️☺️,
I’ll see you again for the April edition of Récap’IT.
April was a busy month in the public sphere, and the lessons learned extend far beyond the scope of public sector IT departments.
The 2026–2027 Interministerial Roadmap on IAM and Post-Quantum Cryptography; hacks of ANTS and EduConnect due to basic vulnerabilities; the InCyber Forum and the 2026 Barometer on data breaches reported to the CNIL; Strubel’s hearing at the National Assembly on the mapping debt. On the Microsoft front, Entra passkeys are coming to Windows. And in the Zoom Youzer, feedback from Proxiserve.
Enjoy the read!
🗓️ On the agenda today:
Cybersecurity: The Government's Roadmap
👉Go!!
Before we begin, I invite you to follow us ️

The government says it in black and white: the previous roadmap was “hampered by budget constraints.” 2025 saw a string of intrusions, leaks, and unaddressed vulnerabilities across government agencies. The new 2026–2027 roadmap published by the Prime Minister revisits the same initiatives, but with specific deadlines and inspections to ensure progress.
The most critical area for a CIO is IAM. identity a top priority, with Zero Trust on the horizon for the most mature organizations.
Deadlines:
On the administrative side, MFA will be mandatory for all administrators and dedicated workstations for critical IT systems by the end of 2026. Administrative sessions from standard office computers will no longer be permitted. In the cloud, any migration will be treated as a new IT system requiring approval, and cybersecurity clauses will become mandatory in digital contracts by the end of 2026, and by the end of 2027 for those handling sensitive information.
The real news is the inclusion of post-quantum technology in the timeline: an inventory of data that will remain sensitive long-term by the end of 2026, limited deployment across IT systems by the end of 2030, and, starting from that date, no encryption products will be available without post-quantum algorithms. The "harvest now, decrypt later" approach is being taken seriously.
For CIOs in the public sector and government contractors, the message is clear: the coming quarters will be aligned with these dates, not with your own cycles. One question remains that the document does not address: there are no figures regarding the resources allocated to meet this timeline. The previous roadmap failed due to a lack of funding. This one makes no mention of any funding.
Source: ANSSI


Receive the best IT news of the month.
Market trends, IT trends, cyberattacks in France... a summary of the news
A 15-year-old teenager, known by the handle "breach3d," was arrested in Corsica in late April. Among his haul were the ANTS system and 12 million lines of personal data put up for sale on cybercriminal forums. The entry point: an IDOR flaw, a vulnerability documented for decades, which ranks among the industry’s most well-known application flaws. Not a zero-day. Not an APT. A server-side authorization control flaw—exactly the kind of thing a basic audit would detect.
EduConnect, same story. The compromise of an authorized staff account in late 2025 allowed attackers to download data on several million students over a two-day period in December, via a vulnerability identified that same month but exploited before it could be fixed. The ministry has since “strengthened” access with two-factor authentication, which amounts to acknowledging that it did not exist on an account granting access to student credentials. Add to that the hacking of the Compas HR software in late March, and the sequence becomes a case in point.
Sébastien Lecornu announced that 200 million euros had been allocated as an emergency measure following the ANTS incident. It’s a classic reaction: we don’t pay for the fix before the problem arises; we pay for the Band-Aid afterward. The timing is telling; the 2026–2027 interministerial roadmap published a few weeks earlier remained silent on funding, while calling for the elimination of generic accounts by June 30, 2026, and the MFA for administrators by the end of 2026.
For a CIO, the message is clear: when a teenager using a script stumbles upon a common application vulnerability and compromises 12 million records, it’s not the attacker’s sophistication that’s at issue. It’s the lack of code reviews, application audits, and governance of privileged access. The 200 million are coming. The skills to implement them, the timeline for integrating them, and the technical debt accumulated on aging IT systems—these are not matters decided by the Cabinet.
Source: Numérama, education.gouv, Le Point


8,613 personal data breaches were reported to the CNIL between September 2024 and September 2025, compared to 5,919 a year earlier. That’s 24 breaches per day—almost one every hour. The 2026 InCyber Barometer, produced in collaboration with the CNIL and Hexatrust, opens the Lille edition of the trade show with a stark finding: the number of victims has surged by 53% in one year, affecting 12.2 million people. Each breach is having a broader impact.
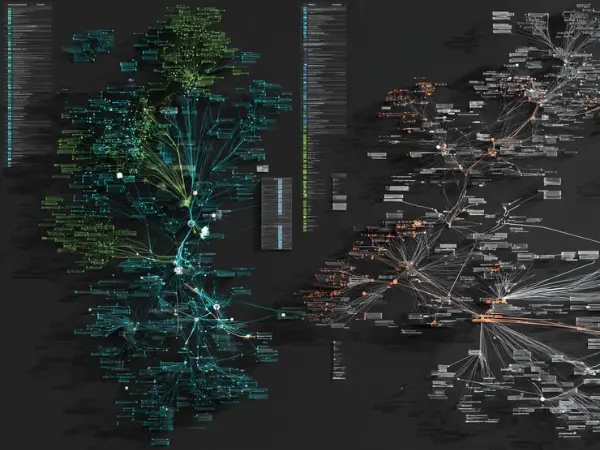
The 2025 Incident Map does not depict futuristic cybercrime. It documents the recurrence of familiar patterns: compromised service providers, hijacked legitimate accounts, missing or bypassed MFA, and poorly governed cloud environments. Conforama, Bouygues Telecom, France Travail, the CAF, the Ministry of the Interior, hospitals in the Hauts-de-France region: the 2025 list covers all sectors. Attackers have moved away from opportunistic targets toward hubs—those ultra-centralized platforms where a single vulnerability opens the door to millions of profiles.
Vincent Strubel, Director General of ANSSI, struck a strong tone in his opening remarks. He highlighted the disconnect between an increasingly tense geopolitical landscape and a digital sector that is not keeping pace, citing “security flaws at every level.” AI is not a magic solution; “betting everything on these kinds of tools would be a mistake.” The cloud also came under fire, with Strubel noting that we have “cut corners” by outsourcing security. NIS2, whose French implementation is behind schedule, is set for a second reading in July. ANSSI urges that we wait no longer.
For a CIO, the barometer confirms what reports have been saying for the past three years: the sophistication of attacks is increasing at a slower rate than the recurrence of the same organizational weaknesses. Poorly managed third-party access, passive detection, and failing privileged account governance: these are choices, not inevitabilities. And the fact that the opening session of the European Digital Dependency Forum was sponsored by the American company SentinelOne is also a key point in the debate.
Source: LeMondeInformatique, ITPro, JDN, ITSocial


During his testimony on April 30 before the parliamentary commission of inquiry into vulnerabilities in France’s digital infrastructure, Vincent Strubel, Director General of ANSSI, offered an assessment that goes beyond the realm of software alone. “No one today has a complete map of their software environment—neither the government nor businesses.” And the following statement hits hard: "Generally speaking, the cyberattacker knows the victim’s information system better than the victim does."
The report focuses on third-party components, software dependencies, and open-source software embedded in commercial products. Strubel cites the European Cyber Resilience Act as the first attempt at traceability, noting in passing that “we now have much more reliable information when we buy a sausage than when we buy a digital solution.” The metaphor is tongue-in-cheek, but the assessment is not.
But the mechanism described goes far beyond the software supply chain. When it comes to identities, the same blind spot exists. How many organizations know exactly how many accounts exist in their IT systems, who they belong to, what permissions they have, and which machine identities are running in the background without an identified owner? The 2026–2027 interagency roadmap requires the elimination of generic accounts by June 30, 2026, and an annual review of administrative privileges. Without a prior inventory, these requirements are unenforceable.
For a CIO or IAM manager, the Strubel hearing highlights an operational reality: mapping debt is the root cause of all other cybersecurity issues. An attacker methodically scanning a poorly documented IT system moves faster than teams discovering their own orphaned accounts in the midst of an incident. The question to ask isn’t “are we protected,” it’s “do we know what needs protecting.”
Source: LCP
Would you like to receive our white paper on identity and access management?

At the InCyber Forum, ANSSI and Cigref released a joint report on digital security governance, making their position clear from the very first sentence: "There is no single universally valid model. " No top-down standards, no off-the-shelf framework. Instead, there are four archetypes, and it is up to each organization to determine where it fits.
The first, "expert and partner," places security as close as possible to the business units, early in the project lifecycle, in a facilitating role that mediates without hindering progress. The second, "compliance and public affairs," structures the function around standards, regulatory risk, and relations with authorities. The third, "platforming and governance," positions it as a cross-functional role that pools capabilities and clarifies the distribution of responsibilities. The fourth, "integrated security," embeds it directly into business operations and covers the continuum of prevention, detection, and crisis management.
The report then shifts its focus to the mechanisms involved: who makes decisions, who acts as an arbitrator, and who is accountable. This is where the practical value comes into play.
For a CIO or CISO, the useful approach is to clearly position oneself within one of these four models. Many organizations straddle two approaches, with a security function that provides both business advisory services and ensures regulatory compliance, without anyone having decided who is in charge of what. This ambiguity dilutes responsibilities and hinders decision-making when it matters most. The report does not say which model to choose. It says that one must be chosen.
Source: Digital Solutions

Microsoft is rolling out general availability support for Microsoft Entra passkeys on Windows. The rollout will begin in late April 2026 and will be completed by mid-June across all environments, including both company-managed devices and personal or shared devices, even those not connected to Entra.
The method is based on the FIDO2 standard. Passkeys are device-bound, stored in the local Windows Hello container, and authentication is performed using facial recognition, a fingerprint, or a PIN. They are resistant to phishing by design, unlike traditional passwords. This applies to organizations using Microsoft Entra ID with passkeys enabled in the "Authentication Methods" policy, with additional control possible via conditional access policies.
Good to know: Microsoft Entra passkeys on Windows no longer require explicit authorization by adding Windows Hello AAGUIDs to the whitelist of a FIDO2 passkey profile—a requirement that was in place during the public preview.
Source: IT Connect


Proxiserve, an energy services group with 4,300 employees, has deployed Youzer to automate identity management across its entire application stack. The catalyst: a three-year phased migration to SaaS that brought to light a structural pain point—the manual management of new hires, transfers, and departures in an environment of high employee turnover.
The platform is currently connected to 4 corporate directories, 3 email systems, 4 HRIS systems, Salesforce, and several business applications, for a total of 44 active connectors within the scope. The workflows cover the entire lifecycle: automatic assignment of profiles upon arrival based on the position and functional scope, notification of the relevant managers, and systematic deactivation of access upon departure without requiring an IT ticket or an HR request.
Operational results: 200 transactions processed each month without manual intervention. In terms of governance, assigned permissions correspond to actual roles, access is automatically revoked upon departure, and authorization history is fully traceable. The project continues to be rolled out to the group’s subsidiaries.
Sylvain Bourdette, CIO of Proxiserve: "Standardizing and automating intake and discharge processes was a top priority in our transformation plan."
Source: IT Social

Thank you for reading me this far!
Any feedback, want to discuss a project?
I'm here for that 👋.
👉Reply to this newsletter
We've sent you the newsletter and you think it's great? Sign up here 👇
Sharing this newsletter is what keeps it alive!
Every month I send you my discoveries, my analysis on IT news.
I do a lot of monitoring and I share it all!
I'm Mélanie and I'm Youzer's marketing manager.
About me? I have an unquenchable thirst for learning! I'd rather read a book 100 times than watch a movie. I'm a fan of HP 🧙🏼.
I do running and collective sport roller (don't look for it, it's dangerous).