
Hello ️🌼,
I’m back with the April and May edition of Récap’IT. Yes, I’m running late 🙈—I’m in the middle of a major redesign of the Youzer website and have less time to devote to other projects. So this newsletter is exceptionally long.
Enjoy your reading!
📅 Today's agenda:
👉 Go !!
Before we start, I invite you to follow us 👉️

5,629 data breaches in 2024, a 20% increase in one year. And already 2,500 incidents reported in the first quarter of 2025 alone. This is the chilling assessment presented by the CNIL in its annual report. After months of passively enduring cyberattacks affecting millions of French citizens, the authority is finally taking the initiative: two-factor authentication (2FA) will no longer be merely “good advice”; it is becoming a legal requirement for databases containing more than 2 million people.
In the crosshairs: telecom operators, e-commerce platforms, public services, and any organization that collects large amounts of data. In other words: just about everyone.
80% of large-scale data breaches could have been prevented with a simple one-time password. Most data leaks stem from classic phishing: a stolen password, unprotected access, and millions of records are gone. In critical sectors like finance and healthcare, two-factor authentication is already the norm. But elsewhere, in the absence of a clear requirement, many have chosen to do without it. The result: gaping security holes, and a CNIL that has finally decided to crack down.
Effective immediately, remote access to major databases must be protected by two-factor authentication: a code, a physical key, a dedicated app, or biometrics. Employees, contractors—everyone is affected. 2025 will serve as a transition period. In 2026, enforcement will begin. And those who drag their feet stand to face serious consequences.
What CISO’s have been calling for for years is finally becoming mandatory: two-factor authentication (2FA) is moving from a best practice to a minimum standard. The CNIL wants to go further by strengthening data breach detection and team training. It remains to be seen whether companies will get ahead of the curve… or wait until they hit a wall.
Sources: LeMondeInformatique


On September 29, 2022, everything came to a standstill at Jules. Websites were down, the warehouse was paralyzed, and 500 stores were cut off from the IT system… The group fell victim to a massive cyberattack, triggered by a compromised partner. This wasn’t just a production incident: the group’s entire digital ecosystem collapsed.
Florent Plonquet, the group’s Chief Information Security Officer (CISO), had, however, sounded the alarm. Upon his arrival three years earlier, he conducted a comprehensive audit of the IT system, which revealed outdated infrastructure, poor-quality data, inadequate security, and a corporate culture blind to cyber risks. He then presented a three-year transformation plan, which was deemed too ambitious… until reality hit hard. A week after the presentation, the system went down.
The cost of this cyberattack? Several million euros in remediation costs, tens of millions in lost revenue due to a month-and-a-half-long halt in logistics operations, not to mention the lasting loss of market share. “I had a modest budget to begin with, but after the cyberattack, it ballooned,” Plonquet notes matter-of-factly.
This experience highlights the challenge of calculating ROI in cybersecurity. After all, how can you convince people to invest in an invisible threat? Franck Chemin, CISO at Crédit Agricole Alpes Provence, puts it bluntly: “The challenge is estimating the losses we’ll avoid when everything is going well.” He points out that no one asks for a ROI when installing fire extinguishers—so why should it be any different for cybersecurity?
Nadège Reynaud, Director of Cybersecurity at STET, advocates for a shift in mindset: stepping out of the office, identifying the key assets that drive the company’s value, and developing a business-oriented narrative. It’s less about numbers and more about the perception of actual risk. The more mature a company is in its risk management, the more effective—and credible—this approach becomes.
But the key to success lies in people. You need to be able to pitch a cybersecurity project in two minutes flat, capture the attention of a busy executive, and demonstrate that cybersecurity isn’t a cost center, but a driver of resilience. Forget Excel spreadsheets, forget even PowerPoint slides: trust is built through direct dialogue. And sometimes, in the heat of a crisis that could have been avoided.
The bottom line? If you haven’t been attacked yet, that’s good news. But don’t count on a ransomware attack to free up your budget. The best time to talk about security was yesterday. The second-best time is now.
Source : LeMagIT


I’ll spare you the 100 pages of ANSSI’s latest activity report, but not the key takeaways. Because while 2024 was an Olympic year for sports, it was also one for French cybersecurity. Behind the scenes, the Agency orchestrated a mobilization on an unprecedented scale to secure the Paris Olympics, proving one thing: when the cybersecurity ecosystem prepares seriously, it works. No major incidents to report, despite 548 recorded cybersecurity events. Lesson #1: Resilience is built before a crisis, not during it.
But the Olympics shouldn’t obscure the bigger picture. At the same time, ANSSI handled more than 1,300 incidents—a record—representing an 18% increase compared to 2023. CERT-FR identified 39 confirmed intrusions and assisted numerous victims of ransomware attacks. All of this took place against a backdrop of persistent threats linked to state-sponsored actors (APT28, APT31, Lazarus, etc.) and cybercriminals who continue to target government agencies, international organizations, and local authorities, with a growing interest in subcontracting SMEs.
On the regulatory front, 2024 marked the transition to the new European cybersecurity landscape. NIS2, the Cyber Resilience Act, the revision of eIDAS, the implementation of the 2024–2030 Cybersecurity Act… everything is moving faster. ANSSI is adapting accordingly, by creating a dedicated unit for audits and equipping organizations with new portals such as monespacenis2.cyber.gouv.fr. If you’re still unsure whether this applies to you, now is the time to check.
On the technological front, ANSSI is making headway in several critical areas: generative AI (with a widely noted guide released in April), post-quantum cryptography (with European initiatives led in part by France), and sensitive cloud hosting (with clear recommendations to use SecNumCloud). Also worth noting is the growing influence of regional CSIRTs, which handled 700 cyber incidents in 2024. Local networks are becoming strategic.
This 2024 report confirms one thing: we have moved beyond the awareness-raising phase. Cybersecurity is no longer a “side issue,” but rather a cornerstone of business continuity, sovereignty, and competitiveness. For CIOs, CISOs, and IT decision-makers, this means advancing in maturity across three key areas: regulatory anticipation, technical hardening, and operational coordination. The government is setting the pace. It’s up to us to keep up.
Source: ANSSI

Receive the best IT news of the month.
Market trends, IT trends, cyberattacks in France... a summary of the news
The warning is subtle but extremely serious: the CVE (Common Vulnerabilities and Exposures) program, a central pillar of the global cybersecurity ecosystem, has been temporarily saved until September 2025. Beyond that? Total uncertainty. What is threatening to collapse is nothing less than the foundation upon which global vulnerability management rests. And Europe, though dependent on it, is currently merely a bystander.
CVE is the common language for vulnerabilities. Created in 1999 by MITRE and funded by the U.S. government through CISA, it assigns a unique identifier to every documented vulnerability. Thanks to CVE, detection tools, security bulletins, vulnerability scanners, CSIRTs, and software vendors all speak the same language. It provides a foundation for interoperability without which chaos would ensue. Today, more than 2,000 new vulnerabilities are registered there every month.
The problem is that U.S. government funding is set to end. And despite a budget extension through the fall of 2025, no long-term solution has yet been proposed. MITRE has not ruled out scaling back operations or even partially suspending the service.
And what about Europe in all this? A bystander, yes, but not a silent one. ENISA (European Union Agency for Cybersecurity) sounded the alarm in a statement as early as March 2024. It warns of the EU’s structural dependence on non-European critical infrastructure, controlled and funded by a single country. A geopolitical vulnerability that is becoming increasingly difficult to ignore in the current context.
Because, in reality, European CERTs, cybersecurity providers, and businesses all rely on the CVE. And no one—not even Brussels—has proposed a credible alternative or a Plan B. Launching a European registry? Too time-consuming, too costly, and too risky in the short term. Financial support? Nothing concrete has been proposed so far.
This imbalance places Europe in a position of significant strategic vulnerability. Relying on the United States for the database of all known software vulnerabilities, without any governance leverage or budgetary control, means accepting the political decisions of a third party. And this dependence is no longer consistent with Europe’s stated ambitions for digital autonomy.
In practical terms, without CVE:
Security vendors will lose their common framework.
Vulnerabilities may be identified and named inconsistently, which will prevent correlations from being established.
CIOs will become less effective at prioritizing and addressing issues.
Finally, nations will see their cyber sovereignty weakened.
This isn't just an open-source project at risk: it's a critical global infrastructure—invisible but indispensable.
This article was written in April; Europe didn't take long to respond—see the following article!
Source: Le Monde Informatique

The timing is anything but coincidental. On May 13, Europe reached a strategic milestone with the official launch of the European Vulnerability Database (EUVD) by ENISA. This new public and interoperable database is not simply a clone of the CVE; it aims to address the specific needs of the European digital market by strengthening its cybersecurity sovereignty.
The EUVD centralizes vulnerabilities affecting digital products and services used in Europe, in accordance with the requirements of the NIS 2 Directive. Unlike CVEs, which are deeply rooted in the U.S. ecosystem, the EUVD reflects a clear commitment to autonomy. Designed for the European market, it centralizes data from multiple sources (CERTs, vendors, open source) and enriches it with concrete information: remediation measures, exploitation status, and technical details on the affected products.
This is a clear signal: Brussels wants to regain control over vulnerability identifiers and no longer rely exclusively on Washington.
Also on the agenda is the Cyber Resilience Act (CRA), which, starting in September 2026, will require manufacturers to report actively exploited vulnerabilities through another platform: the Single Reporting Platform (SRP). The EUVD, for its part, will retain an informational role, but its complementarity with the SRP points to a future comprehensive European ecosystem for vulnerability management.
It remains to be seen whether the EUVD will be able to convince publishers, CERTs, and integrators to embrace transparency and interoperability. ENISA anticipates a phase of continuous improvement in 2025, driven by user feedback. We hope so: without active support from market players, even a sovereign database will be only as valuable as the data fed into it.
At this stage, what Europe is proposing is ambitious, well-structured, and potentially revolutionary for those who manage vulnerabilities on a daily basis in multi-vendor environments. If you are a CISO, system administrator, or CIO, you will need to closely monitor EUVD feeds and begin integrating this data into your risk management processes. Because in the future, the criticality of a patch may no longer be determined by a CVE identifier, but by an EUVD tag.
Source: L'Usine Digitale

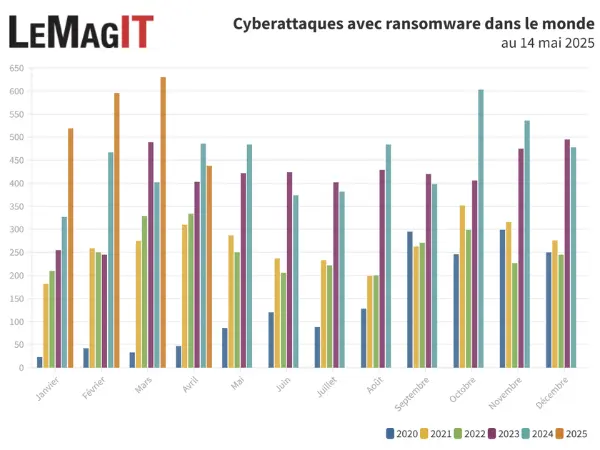
On the surface, April 2025 appeared to mark a pause in the escalation of cyberattacks, with 438 cases reported worldwide compared to 630 in March. But beware of the typical end-of-month blind spot: many claims are reported several weeks late, which temporarily skews the figures. March initially recorded 480 incidents before being revised to 630.
The chart above illustrates this: over the past four years, the trend is clear. Even with only partial figures available, 2025 is already on track to match the record levels of 2024. And the underlying trend is upward. France is no exception. In April, Cybermalveillance.gouv.fr recorded more than 130 requests for assistance related to ransomware (excluding individuals), a high volume even though it was down from January.
The threat is evolving, diversifying, and shifting. New groups like Crypto24 and Silent are experimenting with different forms of extortion, while Akira is ramping up its attacks. Is RansomHub fading away? Others are stepping in to take its place. April’s figures give the impression of a lull, but the trends tell a different story: one of an ever-present threat that is constantly changing.
Source : LeMagIT
Would you like to receive our white paper on identity and access management?


Hertz: fell victim to a cyberattack linked to security breaches. The full list is still available: last name, first name, bank details, address, driver's license...
Marks & Spencer: fell victim to a cyberattack that disrupted its click-and-collect services.
Harvest: The financial software company suffered a cyberattack in late February, which has just been claimed by hackers, who are now releasing sensitive information about more than 5,000 companies.
Oracle: Has implicitly acknowledged data leaks following a data exfiltration linked to a breach.
The Hauts-de-Seine department: suffered a massive cyberattack; information and communication systems were shut down as a precautionary measure.
Adidas: suffered a data breach through a third-party service provider.
Dior: announces it has been the victim of a cyberattack—as usual, name, first name... all that stuff, but no bank details.
Coinbase: suffered a data breach affecting 1% of its customers and refused to pay the ransom.
Lockbit: LOL, yes—the ransomware group was hacked, and a link on its website led to a database containing sensitive Lockbit information.
Pézenas Hospital: It was the target of a cyberattack, but the highly experienced IT team quickly halted its spread. No files were affected.
INDIGO Group: the parking, mobility, and urban services company has been the victim of a cyberattack.
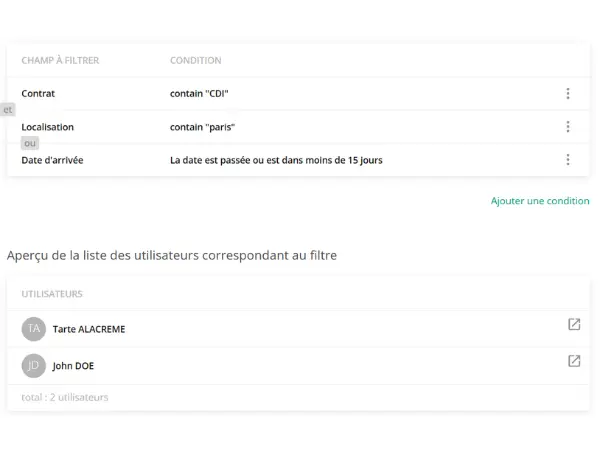
These are powerful tools for managing your accounts and users. In Youzer, custom filters aren’t just for sorting through tables—they’re at the heart of the IAM system.
First, they enable precise targeting. With just a few clicks, you can isolate users associated with a specific application, identify all accounts that haven’t been used in 60 days, or list shared accounts assigned to sensitive services. This level of detail is essential for auditing, remediation, or simply gaining a clear overview.
But where filters really shine is in their ability to detect anomalies. For example:
And that's not all. In Youzer, filters can also serve as action triggers. That's where they become active components of your workflows. Filters act as triggers: whenever a user meets the criteria of a filter, the workflow is triggered for that user.
In summary, filters serve several purposes:
For example ⬇️, this filter can be used to generate a specific list of users or to trigger a workflow as soon as a user meets the filter criteria.
Thank you for reading me this far!
Any feedback, want to discuss a project?
I'm here for that 👋.
Every month I send you my discoveries, my analysis on IT news.
I do a lot of monitoring and I share it all!
I'm Mélanie and I'm Youzer's marketing manager.
About me? I have an unquenchable thirst for learning! I'd rather read a book 100 times than watch a movie. I'm a fan of HP 🧙🏼.
I do running and collective sport roller (don't look for it, it's dangerous).