
Hello ️🌼,
I’m back with the June edition of Récap’IT. Last year I was complaining about being cold, but yesterday, with temperatures hitting 42°C in the shade, I was definitely feeling the heat 🥵.
In the last newsletter, I mentioned a major redesign project, and now several pages of the Youzer website have been revamped! I’m looking forward to your feedback: 🤩😊😐🫤🤢.
Enjoy your reading!
📅 Today's agenda:
👉 Go !!
Before we start, I invite you to follow us 👉️

16 billion passwords out there: what if your MFA is nothing more than a band-aid on a wooden leg?
It’s official: 2025 has brought us yet another data breach of record proportions. This time, Cybernews researchers uncovered 16 billion passwords spread across 30 separate databases, some containing as many as 3.5 billion credentials. A massive compilation derived primarily from infostealer malware—those stealthy agents that siphon off tokens, cookies, and access credentials on the fly.
The real problem isn’t so much the quantity as the quality: this data is recent, structured, and directly usable for targeted attacks—phishing, BEC, ransomware, or bypassing MFA using session cookies that are still valid. A Cybernews researcher puts it bluntly: “This isn’t just a data breach. It’s a large-scale exploitation campaign .”
In this context, companies need to rethink their approach. Here are three urgent lessons:
The era of static credentials is coming to an end. What this massive data breach shows us is that we are no longer dealing with isolated incidents, but with the industrial-scale exploitation of compromised credentials. At this point, continuing to rely solely on passwords and MFA is like equipping your guards with crossbows to face an army of drones.
Source: Cybernews


Receive the best IT news of the month.
Market trends, IT trends, cyberattacks in France... a summary of the news
Microsoft has decided to take a hard line following the CrowdStrike incident last March, which crippled thousands of computers worldwide. The focus is on access to the Windows kernel—long tolerated for antivirus vendors but now considered a risk vector. Starting in July, an experimental version of the Windows Endpoint Security Platform will be tested with members of the Microsoft Virus Initiative program. The goal: to enable vendors to develop solutions that run entirely outside the kernel.
This paradigm shift is nothing new. Back with Windows Vista, Microsoft had already attempted to restrict access to the kernel using PatchGuard technology… before backing down under pressure from Symantec and others. But this time, the situation has changed: Microsoft is pursuing a clear strategy, backed by its Windows Resiliency Initiative, announced in November 2024.
This initiative is based on four pillars:
Another interesting component of this strategy is Quick Machine Recovery, a technology currently being tested that would enable automatic restoration via Windows Update in the event of a boot failure.
Ultimately, this represents a profound shift for security solutions: they will have to operate inuserspace and can no longer rely on integration deep within the system’s core. CrowdStrike is already concerned that its Falcon EDR will lose effectiveness against attackers with elevated privileges. But for Microsoft, this is the price to pay to make Windows more robust—and, above all, to avoid a repeat of the CrowdStrike incident.
Source: Silicon


Disney and NBC Universal have just brought out the big guns: a joint lawsuit against Midjourney for massive copyright infringement. At the heart of the case are AI-generated images deemed far too similar to copyrighted properties such as Star Wars and the Minions. A legal precedent is emerging—and it could have major consequences for all generative models based on unsourced data.
Midjourney, which reportedly generated $300 million in revenue over two years according to the lawsuit filed in Los Angeles, is accused of ignoring several prior warnings. The studios are now seeking not only the return of the revenue generated, but also $150,000 in damages per copied work. If the courts rule in their favor, the precedent could have a seismic impact on LLMs and generative AI tools—not only in the realm of images, but also in text and audio.
Until now, Midjourney has maintained that users alone are responsible for the content generated. But with an AI system trained on billions of images without the explicit consent of the rights holders, that argument seems hard to sustain. If the court rules in favor of the plaintiffs, the entire generative AI ecosystem may have to rethink its foundations.
If we were to draw a parallel with our own industries, this type of case serves as a reminder that AI tools cannot be adopted into information systems blindly. We must ensure that the tools used fully comply with copyright laws, particularly with regard to the data used to train them. Compliance will no longer be a secondary concern, but a prerequisite.
Source: Siècle Digital


Often viewed as a regulatory burden, the GDPR now reveals a far more strategic aspect: that of an economic shield. According to a study by the CNIL, the regulation is estimated to have prevented between 90 and 219 million euros in losses related toidentity theft in Franceidentity . These savings directly benefit businesses in 82% of cases. And while the estimate remains theoretical, it is based on concrete figures: 200,000 people fall victim toidentity theftidentity year, according to the Ministry of the Interior. Better yet, the GDPR has had a ripple effect: between 2015 and 2019, the percentage of companies updating their security protocols rose from 14.2% to 18.3%. Admittedly, this momentum has since slowed (12.1% in 2022), but in the face of the explosion of AI-fueled threats, investment in compliance and cybersecurity could well become a priority once again—both strategically and financially.
Source: CNIL

Would you like to receive our white paper on identity and access management?

Disneyland Paris: Sensitive data was hacked, a ransom demand was made, and the data was published a few days later. The data in question includes maps, videos, photos, and private messages...
Sorbonne University: For the third time in a year, the university has posted a press release on its website stating that it has been the victim of a cyberattack. Email addresses, bank details, Social Security numbers, and other personal information have been compromised.
The Ministry of Education, the Tax Authority, the Ministry of the Interior...: An infostealer was used to collect 190,000 usernames and passwords, and the files were leaked.
Center Parc: The telephone reservation system was targeted, exposing the personal data of approximately 20,000 customers.
International Criminal Court (ICC): The ICC has detected a sophisticated and targeted cyberattack, the second in two years. The incident was quickly contained, but an impact assessment is currently underway.
Cloudflare: recorded the most powerful DDoS attack in history. Launched from more than 120,000 IP addresses across 161 countries, the cyberattack flooded the targeted servers with 37.4 terabytes of data in less than a minute.
Hawaiian Airlines: The airline has confirmed a cybersecurity incident that has not affected its flights or reservations.

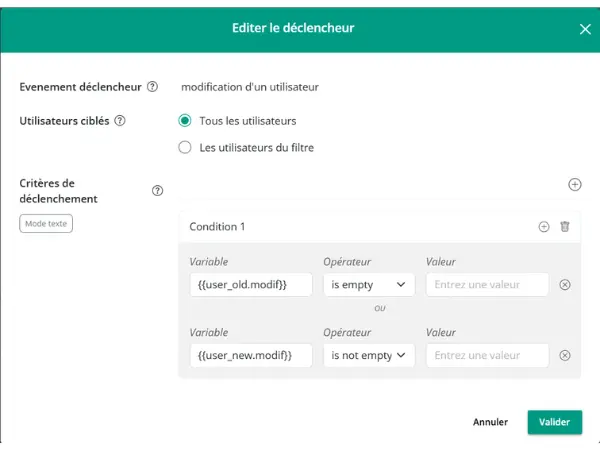
With Youzer, you can now trigger a workflow simply by modifying a specific user field. No more need to monitor the entire HR directory—we’re talking about highly targeted alerts.
A contract renewed at the last minute? A departure date postponed? A last name updated following a marriage?
Whenever a relevant change occurs (contract, date, email, etc.), a workflow can be triggered automatically.
A real-world scenario: A user is marked as leaving, their access is suspended, but HR receives the information the day before their departure—and they end up staying. The date is changed, and just like that, the workflow kicks in to reactivate all relevant accounts.
Another use case: assigning new access permissions and rights to a user following a temporary or permanent job change — Youzer automatically recalculates permissions to verify alignment in real time.
Thank you for reading me this far!
Any feedback, want to discuss a project?
I'm here for that 👋.
Every month I send you my discoveries, my analysis on IT news.
I do a lot of monitoring and I share it all!
I'm Mélanie and I'm Youzer's marketing manager.
About me? I have an unquenchable thirst for learning! I'd rather read a book 100 times than watch a movie. I'm a fan of HP 🧙🏼.
I do running and collective sport roller (don't look for it, it's dangerous).